Article Updated: 22 Jun 2022
Update: (March 2022) Google has started sending global email notifications to all Gmail account owners that on May 30 (that’s less than 3 months from now) you may lose access to apps that are using less secure sign-in technology.
Essentially, as we predicted last year, Google is now forcing users to either use sign-in with Google Account, OAuth 2.0 or, alternatively, 2SV authentication technologies. Read further below to learn about 2SV in more details.
From what we understand following this Google Help article, you will still be able to use your favorite email app, but if it falls on the Google’s list of “less secure apps” (such as Outlook 2016, Outlook 2010, Outlook 2007 and older, including some other email apps/software), you will have to switch to 2SV authentication, namely, 16-digit app password, as explained in our guide below.
*
Update: (June 2022) Google has finally blocked access to insecure apps. Now, if you still wish to continue using such apps, you must enable and use new method described in this article.
Google is pushing 2SV (2-Step Verification – not to be confused with 2FA, they aren’t the same thing – differences explained below) and starting from November 1, 2021 it will be mandatory for all YouTube Creators who monetize their channel(s) and are part of the YouTube Partner Program (YPP). They are the first group of Google account holders that is affected by this change, and we can expect more related news in the upcoming years months.
What does this mean for 3rd party apps like Microsoft Outlook, Mozilla Thunderbird, other Email clients, Contacts, Calendars, and other 3rd party apps by independent developers? Should you stop using them and switch exclusively to Google products?
First things first: let’s clear up the confusion and get straight with the terminology!
2SV (2-Step Verification / Two Step Verification)
What is 2SV?
2SV is a second layer of security when you sign-in (login) into your account, e.g. a Google Account, Gmail, YouTube, Microsoft Outlook, Amazon AWS, or some other service.
What this means is that username (and/or email) and password are no longer enough to complete the login procedure, and you must add an additional independent way of verification that it is really you who tries to access a particular service.
The most common example of 2SV is by adding your cell phone number in order to receive a secret code via SMS message or automated phone call that you must enter AFTER you submit your correct username/email and password combination.
This is why it is called “2SV” — because it uses two independent connections, devices and apps to verify true account holder.
What if you do not have a cell phone or you simply do not wish to submit one?
This depends on the company that provides and enforces 2SV service, but usually you can add a secondary email address as a backup, which does not belong to the same company / domain. For example: suppose that you have 2SV enabled for your Google / Gmail account, but in order to set it up you must add another email from Microsoft, Yahoo, ProtonMail or whatever 3rd party / independent company email you use. This way, instead of receiving SMS message on your phone, you will receive a secret code on your secondary email account, which is required to complete signing in process and gain access to your account.
What are the benefits of 2SV?
If your original password becomes compromised, the perpetrator still won’t be able to access your account, even if it knows your username and password, because a new device must be authorized first using a secret code sent to your phone or other email account!
2SV is required when you sign into your account and try to modify sensitive information, for example, when you try to sign in to your Google account, change phone number or recovery email address.
What are the downsides of 2SV?
Apps that do not support 2SV may be left “out of the loop” and locked out. Thankfully, Google provides support (for the time being) for such apps and scenarios, so you can still continue using them.
Another downside is the fact that 2SV is essentially just another secret code / password user needs to use for verification, and even that second method may be compromised (e.g. your phone gets stolen, access to all your emails become compromised at the same time etc.). In such cases 2SV protection is useless, unfortunately.
User must be aware of the risks involved and be careful where it leaves its data, which services and companies it trusts, but sometimes things may get out of control (e.g. virus infection, malware attack, phishing etc.), rendering even the best 2SV system innefective.
2FA (2-Factor Authentication / Two Factor Authentication)
What is 2FA?
2FA differs from 2SV in such a way that instead of receiving another secret code (which is essentially just another password) by another email account or phone (which both can be compromised as well) you must provide some unique method that only you can posses or have – for example, a fingerprint scan, an iris scan, DNA sequence, a secret USB dongle key etc. 2FA authentication is required each time you try to access your account.
What are the benefits and downsides of 2FA?
Even this security method, which is much more secure than 2SV, can be compromised, and you cannot change your fingerprint or iris patterns later.
Iris patterns change in our eyes over time as new studies confirm, making iris scans over long periods of time unreliable verification method. Same holds true for fingerprints, damages to our skin and organs can affect this method, as well.
USB dongles can become lost, making the verification later impossible, unless you have another copy. Data can expire or become corrupted, controllers that act as an interface between flash memory and communication device (phone, tablet, computer) can become damaged, as well, rendering USB key practically non-functional, and so on.
But, still, in terms of security, it is considered more secure than 2SV, because under “normal circumstances” it is generally much harder for an enemy to obtain and copy them (but their digital representation is a liability, thus not impossible).
Google Account Two Step Verification – How To Enable Access To Microsoft Outlook, Mozilla Thunderbird & 3rd Party Email Apps
Assuming that you already enabled 2SV in your Google Account, you have by now already discovered that your Outlook, Thunderbird or other email apps stopped working, prompting you to enter “new” password — which you did not change! What can you do to grant access or whitelist those apps in order to keep using them at your home or office?
How To Enable Outlook, Thunderbird and other Email apps to access Google 2SV secured accounts
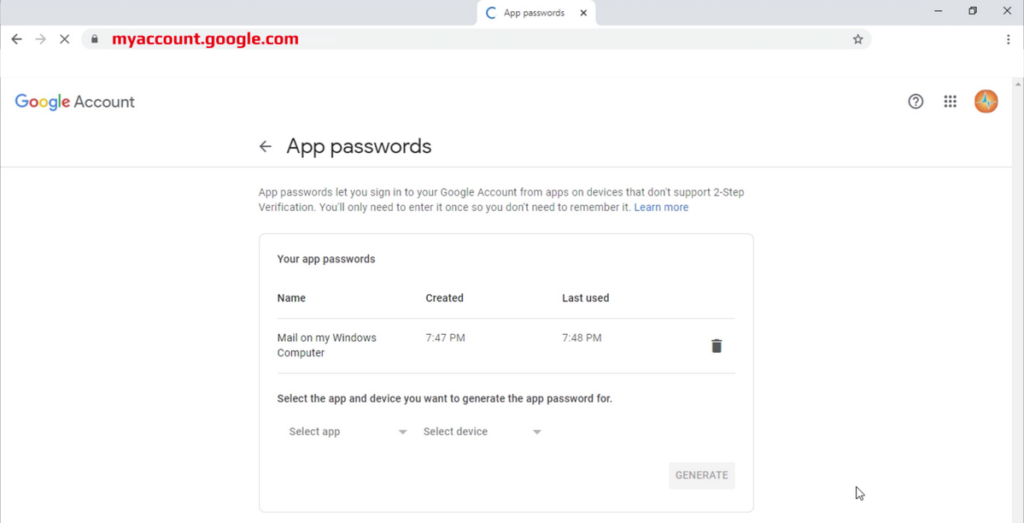
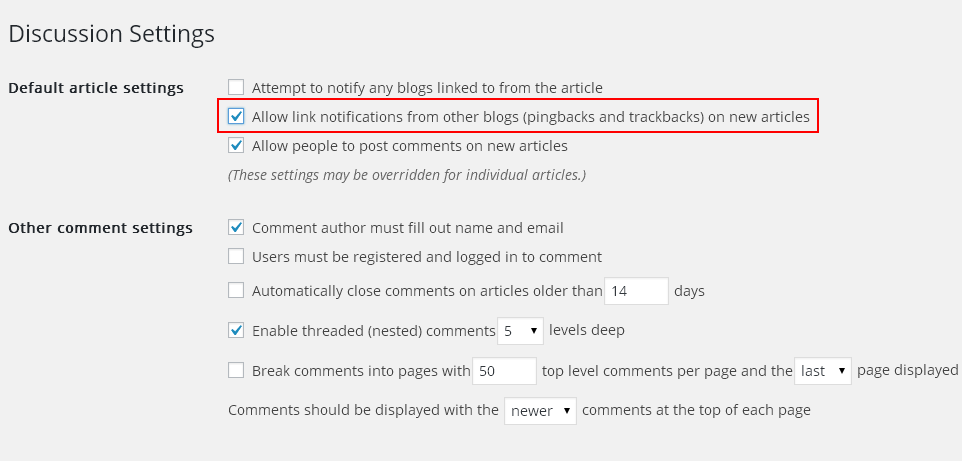
- Login to your Google Account at myaccount.google.com
- Go to Security section
- Scroll to Signing in to Google section
- Activate 2-Step Verification security feature (click or tap on the title) and set your cell/mobile phone number and/or additional email account for signing-in or recovery purpose (for example, in case you lose access to your phone)
- New option will appear after previous step – click/tap on App passwords section
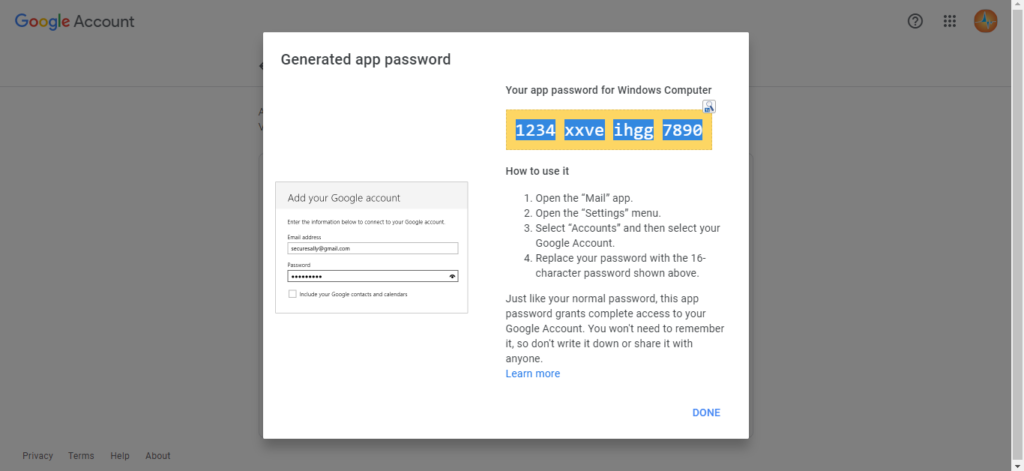
- Generate a password for Email / Contacts / Calendar / Other app you wish to use (be careful to select proper app device type, otherwise it will not work!)
- Copy generated code and enter it as a replacement password in that app!
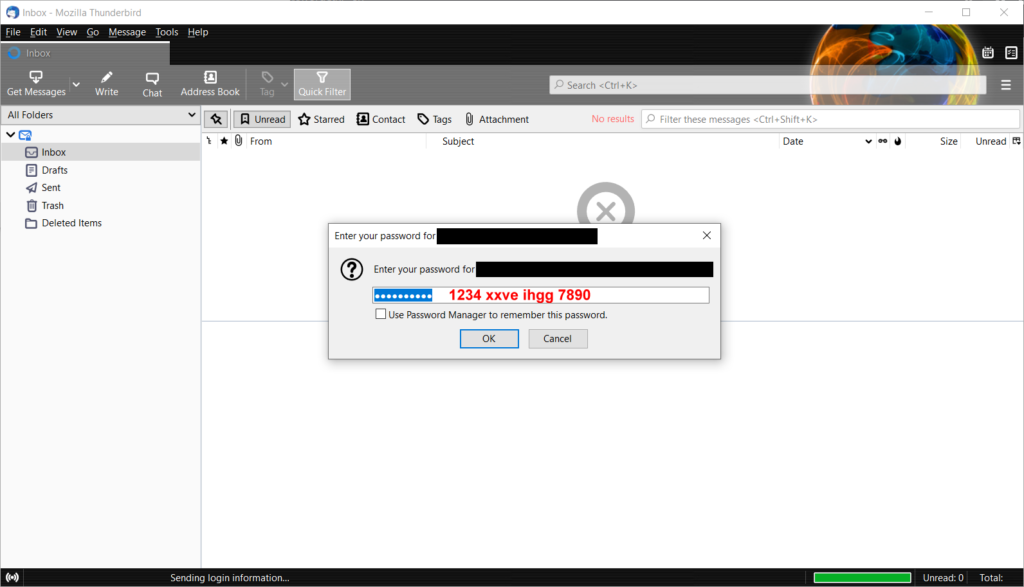
Example for Mozilla Thunderbird:
That’s it! Once you generate an app password, you must use that code instead of your regular Google (Gmail) account password in your 3rd party app. This is the way you can grant access to your Outlook, Thunderbird, Microsoft Windows Email or any other email app.
Confused? Watch video tutorial instead:
CONCLUSION
You probably asked yourself by now what is the point with all this? We replaced one password with another one, and now what?
Well, the whole point was to protect your original Google account, remember? This way, if your email app or some other 3rd party service gets compromised, the perpetrator still won’t automatically gain access to your main Google (Gmail) account!
App passwords are automatically revoked when you change your main Google’s account password (for security reasons). Also, at any given time, you can revoke access to specific apps simply by deleting the generated code(s) in your Google Account’s App passwords section.
The added benefit you might initially miss is that we increased security of our Google account, which may be important defense factor against hacking attempts, ransomware, and other virus infections.
This method does not always ask for secondary authentication, and once you authorize an app with a special access code (or use native apps from service providers such as Gmail by Google) you won’t be bothered again until you change your data or suspicious activity is detected.
There is a risk involved with both 2SV and 2FA authentications. Suppose that you used 3rd party email account for 2SV authentication, which suddenly got cancelled, or your phone number is no longer in use or owned by you – you will also lose access to the 2SV protected account, as well!
Same thing is true with 2FA. If you, for example, lose your USB dongle with secret key, as Randall mocked the idea in his XKCD comic above, you will permanently lose your access, unless there is another way to restore it. This will bring huge painful headaches to the non-techie people.
While this practice will increase accounts security measures, and potentially prevent them from permanent hacking and loss of access, it does have some serious consequences you should be aware of.
- For home users: this is just another annoyance, essentially, despite the fact that it does increase the security.
- For business users: in particular, companies whose employees use free Google Account services (most notably, Gmail service) will potentially be in trouble. For one, the IT managers, administrators or technicians will have to perform all the changes required to set up 2SV in the first place, but also keep track of what alternative channels (e.g. secondary email accounts or mobile phone numbers) were associated with them in case of password change, employee change etc. The information required for later account access retrieval will be essential because password alone won’t be enough.
This is why Google does not yet enforce its business customers (Google Workspace and/or Google Cloud Identity) to follow this change, but they will be at a later date.









![Xiaomi App - How To Re-Install Stock Factory Version - How To Fix Corrupted Gallery App [no root]](https://tehnoblog.org/wp-content/uploads/2025/09/Xiaomi-Gallery-App-Code-Bugs-Artwork-1024x576.png)















11 Comments
Add Your CommentI am so happy I found this article! It resolved my very frustrating gmail authentication Windows 11 mail issue.
December 30th, 2021Well, the other major inconvenience, which is an understatement, is being permanently locked out of your acct out of nowhere, being required to provide an 8 digit backup passcode when logging in on a recognized device using your password.
There NEEDS to be another solution. Google canNOT go inserting itself into everything we do so that we rely on them for everything and then just lock us out of our accts for no reason and say sorry! Cant help you! And cause people to LOSE EVERYTHING! 20 YEARS OF IMPORTANT ITEMS that were saved to Google for safety and security we were promised. How do we protect ourselves from Google ?! Legal documents for lawsuits, mental health paperwork, important files FOR MY LIFE!? My contact for things I’m depending on is no longer valid. My entire life is now jeopardized and pretty much destroyed because of this stupid 2 step verification thing and IT IS ABSOLUTELY UNACCEPTABLE that Google is telling us there is no solution and access is lost forever.
Ive done nothing to warrant this. One day out of nowhere Google suddenly decided I needed to provide an 8 digit backup passcode to access my acct. I don’t have any such thing. Support has been no help at all. Ive done all the things theyve told me to do and tried signing in from a recognized device and theyre still demanding this code i dont have and cannot get. Acct Recovery doesn’t work either. There MUST be a solution. They HAVE TO make one.
Anyone else in this predicament? How does one go about suing Google for this? Is there a class action suit I should know about?
April 19th, 2022Hi, sorry to hear this, I understand your frustration. This happened to my friend, but he was lucky, because he was logged-in on his old computer he wasn’t using anymore. Once he turned it on and went to Google Gmail, he was able to access it, and change Google Account recovery settings – added recovery phone number and backup email account (non-gmail email account).
So, if you happen to have an old PC or phone, where you still have access, this is THE ONLY way to recover your Google/Gmail account access that I’m aware of.
June 17th, 2022I am in the same situation. I have tried literally everything googles help has come up with and I still can’t access my account. And many of these solutions they have end up with use an app password. Login to your Google account go to security, go down to app passwords and generate a new app password to use. Well, am I the only person who is not able to understand? Login to my Google account? If I could do that I would not be going in circles like a dog chasing his tail! Can someone please explain this to me cause it really doesn’t make sense! I’ve been trying to recover my account since I lost cellphone in Nov. 2017!
June 22nd, 2022Hi Lydia, I’m very sorry to hear this, a lot of people seems to be affected by security changes at Google in the past year.
As I replied to K. above, I’m afraid if you don’t have another device where you’re still signed in there is no way to access and recover your account, unless you have previously set a secondary recovery email address or phone number.
June 22nd, 2022We have been learning for some time now that our overdependence on large Silicon Valley tech companies is going to become a disaster for which we have no recourse. Their power over our personal information infrastructure is absolute, and we have absolutely no intrinsic rights when it comes to their decisions about changes they decide to make & enforce.
What we are learning now is that their convenient services were never “free”. They are paid for by surveilling our online lives and selling our consumer profiles & current shopping desires to marketers. We exist on their digital plantation and must obey their rules or be banished.
Good luck trying to sue a company as large & politically connected as Google. The System does not exist to balance the power between consumers and corporate enterprises. The System exists to protect the interests of big money donors to politicians, political parties and PAC’s. To them, we are all ants on their kitchen floor.
April 29th, 2022Have gmail account logged into Thunderbird which is no problem. However if I try to log in on my laptop it wont accept my password. My password is correct!!
May 2nd, 2022Hi, Peter. You must use the code instead of password on your laptop.
May 2nd, 2022I don’t see any “App Passwords” anywhere on the signing into Google page?
June 8th, 2022Hi bob, you must first enable/activate 2SV security feature in your account. The new option will immediately appear under it afterwards.
June 9th, 2022thanks for explaining, i can stop the infinite loop of hammering my google-password into thunderbird/lightning now :)
June 17th, 2022