Android applications for mobile devices are interconnected more than ever before. Many of them use built-in advertising platforms, analytics and other user tracking technologies. In order to increase user’s control of such apps and limit their capability to contact outside world and “phoning home” activities, one should install a firewall app. Here’s how.
How To Limit Android Apps Network Access and Preserve Privacy?
Some apps seriously abuse their advantage over the innocent and unsuspecting end user – you! We wrote about this on numerous occasions, most famous was the incident of an app that caused fake CPU overheating warning messages in order to lure users to click on an advertisement. True story.
Popular messaging apps like Facebook, Instagram, WhatsApp, Viber, TikTok, AliExpress, Amazon shopping apps and alike, literally know your rough location: are you at home, on the move, at school, work… They send tracking requests and other analytics data every few minutes to Amazon AWS, Google Cloud or other 3rd party Computing platforms, you name it. They know more than you think or you are willing to share with them. The most shocking part? Users are completely unaware how much they are tracked (and abused) in this way!
Modern Android versions (11+) have additional feature that might limit their tracking activities, and it has nothing to do with privacy: battery optimizations present and implemented in 3rd party apps will turn off background apps if they aren’t used for some predefined time (but some apps like Gmail are excluded from this and you cannot change the settings manually!). This, however, is not exactly a privacy feature, but more of a consequence of various energy saving efforts to make Android more battery friendly OS.
Google could limit the tracking activity of any app — at least as an option — if they wanted to. What we mean by this? For example, app would be allowed to send tracking, analytics and other data to its servers only while the app is actually being used — e.g. it is in focus as a front screen activity. Granted, messaging / communication apps would be allowed to receive push notifications, in order to provide near real-time communication. But, other apps like shopping portals (Amazon, eBay, AliExpress, BangGood etc.) games, non-critical “offline” tools and so on should be restrained from continuous tracking abuse at all times unless they’re in focus.
With a firewall app you can simulate “no internet connection” mode for specific applications, while all other apps and services have normal access to the internet. This is useful particularly for security reasons, for example, if you are in doubt that a specific app – such as a File Manager app, that may store sensitive information about your FTP server or NAS drive password, may “leak” the data to an unauthorized 3rd party.
You can use a firewall app to limit any Android app spying activity, for example, NoRoot Firewall is an excellent ad-free firewall app for Android OS! There are few others equally good, each offering some unique features, so better try them all and see which one is the best for your needs and workflow.
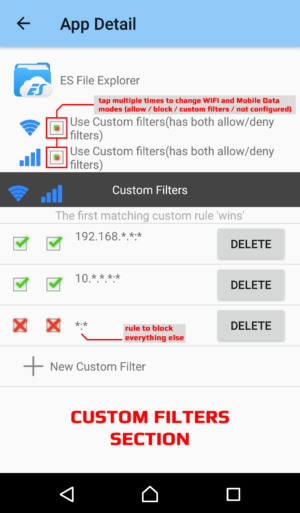
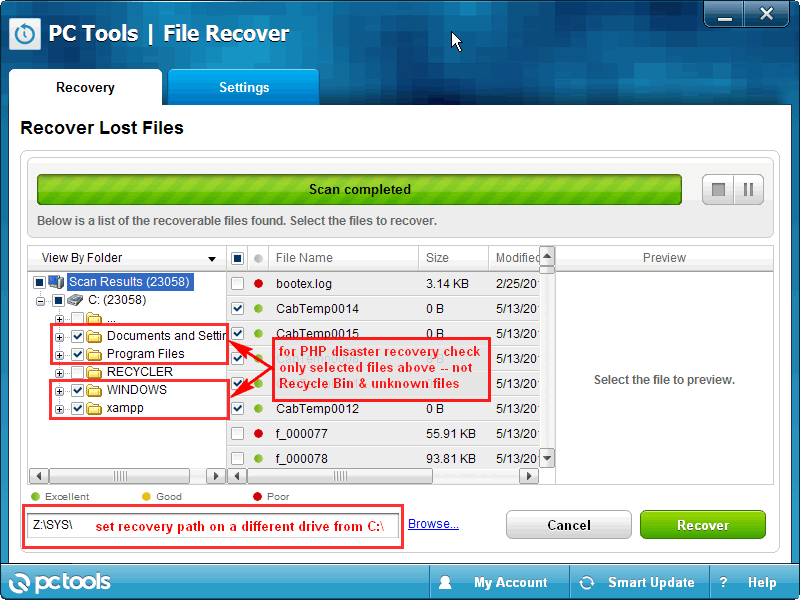
Above is one combined screenshot from NoRoot Firewall, where you can see how many frequent requests (aka “phoning home”) infamous ES File Explorer used to make during start-up and ordinary use. Now, we don’t know what kind of traffic that is, besides usage stats, but we can safely assume that they are probably ad-serving networks (from which apps pull external embedded content), banners, promotions, send usage statistics and crash reports back to developers.
You can block all that with a firewall app! Of course, without root access on Android, firewalls will use less attractive bogus (redirect) VPN connection, which may interfere with some other apps functionality or create short glitches (e.g. ERR_NETWORK_CHANGED in older Chrome mobile browser app – which is now fixed btw.), but this is usually completely harmless.
Note that it is essential to create bypass filters for apps like File Managers or any other app that requires local network access!
NoRoot Firewall app might not work properly on some phones running latest Android versions (we had some issues with several different Xiaomi smartphone devices — solution is to enable under Settings > VPN > NoRoot Firewall app (gear icon) > Always-on VPN along with the off setting for battery optimization (in battery related settings). Still, even with all these options tweaked, NoRoot Firewall keeps closing on its own. After some investigative work, it seems that memory optimizer app kills it, when you switch to recently used apps list and click on it.
Also, you can try other apps in the Play Store in that case. For example, No Root Firewall app by Protectstar Inc. or similar one, although, NoRoot Firewall app by Grey Shirts developer is far less complicated and streamlined for novice users, it is completely free, and our No.1 choice.
How To Install Firewall App For Android
- Visit Google Play Store
- Search for “firewall” and pick your favorite app (NoRoot is great and we use it, for example, but there are many others)
- Install and run it. Accept permissions and create VPN connection (this is required on non-rooted devices, because there is no other way to do it). It will become active instantly and block everything by default. Configure the app to run at system startup / boot every time, and define optional custom rules
How To Define Custom Rules / Filters and Configure Firewall App For Android
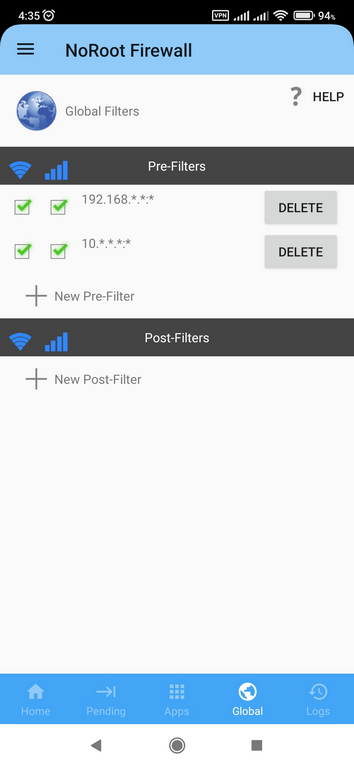
Creating filters (custom rules) in NoRoot Firewall is super easy, and app allows you to combine or mix rules for Wi-Fi and Mobile Data separately.
The main trick here is to allow local network traffic (e.g. 192.168.*.*:* , where part after IPv4 address and colon (:) symbol is port wildcard). Local network traffic is usually safe, and it limits device access to the same Wi-Fi network your device is currently connected to (e.g. your home Wireless Router or Gateway, for example). This way, app will be able to access your home or office printers, other devices, computers, network storage drives, smart TVs etc. but it will be blocked for anything else (e.g. outside world).
NoRoot Firewall app will automatically detect any new app’s intention to access network (either local or remote, it doesn’t matter) and block it by default, until you manually allow it or apply special rules / filter for each particular app.
For example, you need to allow 192.168.*.* IP address and for port select a predefined * (wildcard symbol) from a drop-down menu. And, that’s it!
You can block any other IP address in a separate definition. Optionally, you can bypass other reserved and private ranges, such as 10.*.*.* and 172.16.*.* if required. Everything else you do not use / need should and will be automatically blocked.









![Xiaomi App - How To Re-Install Stock Factory Version - How To Fix Corrupted Gallery App [no root]](https://tehnoblog.org/wp-content/uploads/2025/09/Xiaomi-Gallery-App-Code-Bugs-Artwork-1024x576.png)











4 Comments
Add Your CommentI’ve followed these instructions, and I think I understand how this is working, but one program I love to use called “KDE Connect” still will NOT connect unless the NoRoot Firewall is turned OFF.
August 5th, 2021Please help me…. To get KDE Connect to work over my local network
Come apps cannot work with firewall enabled, so I can’t really help you with this issue. Contact developers and explain the issue, they might be able to help, or at least offer explanation.
I suppose you configured firewall app properly, but you can also try setting up a pre-filter (fourth icon at the bottom) to bypass it on local networks.
August 5th, 2021Hi, this firewall allows input filters? I use a app for php server in the phone, but it’s block input conection.
September 8th, 2022Can you explain a bit what do you mean by “input filters” ?
If you refer to a bi-directional blocking, it either blocks everything or passes everything. It’s not like a router or Windows firewall where you can independently block incoming or outgoing connections.
Also, make sure you properly configured Global Pre- and Post- filters in the app. The order of execution is:
1. Pre filters (rules)
2. App filters
3. Post filters
Also, since it creates virtual VPN connection and routing, you won’t be able to share WiFi access point on your phone with other devices connected to it while the firewall app is running. Maybe that’s the problem in your case. Sorry, I don’t have a solution for it.
September 8th, 2022